Es habitual escuchar afirmaciones tales como: “Linux no tiene Virus“, “Apple no tiene virus“, “Los sistemas UNIX Like no tienen virus“, y aunque se ha escrito y hablado mucho al respecto, yo quiero dar mi opinión personal sobre el tema.
 Bien, pues eso no tiene porque ser del todo cierto, ya que cuando estas personas hablan de virus se refieren mas bien a cualquier tipo de Malware, a la Ingeniería Social, al Phishing, o a cualquier tipo de mal funcionamiento de su equipo, ya sea provocado por alguna tercera persona malintencionada, o un despiste por parte del usuario, y no a un virus como tal.
Bien, pues eso no tiene porque ser del todo cierto, ya que cuando estas personas hablan de virus se refieren mas bien a cualquier tipo de Malware, a la Ingeniería Social, al Phishing, o a cualquier tipo de mal funcionamiento de su equipo, ya sea provocado por alguna tercera persona malintencionada, o un despiste por parte del usuario, y no a un virus como tal.
También he escuchado tales afirmaciones cuando se utiliza un sistema operativo que no es estable, ya que la queja “tengo un virus” ha acabado por convertirse en el “me encuentro mal” para referirse a que al PC de casa le pasa algo, y desconocemos el porqué.
Nosotros mismos podemos ser nuestro mas temible virus si actuamos con poco sentido común, por ejemplo siguiendo el típico tutorial que afirma que la única solución a tu problema es ejecutar el comando rm -rf /* en GNU/Linux o format C: en Windows.
Como explicaba un buen profesor que tuve en una de sus clases, igual que no tomarías cualquier sustancia sin antes informarte sobre sus efectos y riesgos, no deberías ejecutar ninguna orden en tu terminal sin antes haber investigado por tu cuenta que acciones va a tomar en tu sistema, el tutorial solo nos dará un guión de la investigación que debemos llevar a cabo, reduciendo el tiempo y esfuerzo de la misma.
Cierto es que hay sistemas peor hechos que otros, pero eso no significa que por utilizar un UNIX Like y tener sentido común, o comprar todos los productos de seguridad que salen al mercado para Windows estamos protegidos ante todo, aunque algunas empresas vivan de vender ese tópico.
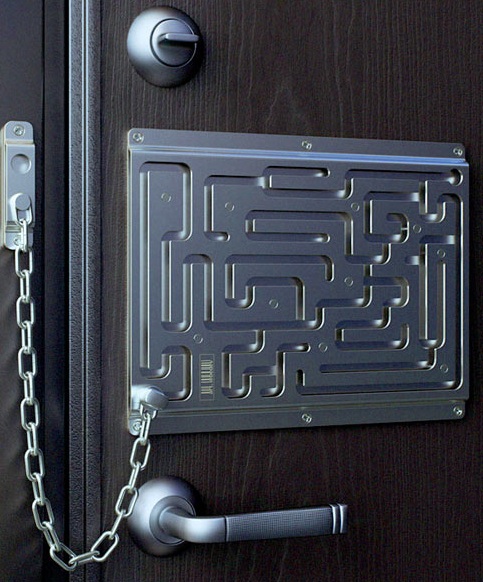
Eso es tan incierto como pensar que por tener una cerradura de seguridad estamos completamente a salvo de los ladrones, por lo que compramos una puerta de aglomerado para invertir el resto del dinero en dicha cerradura, o securizamos al completo la principal puerta de entrada olvidando que existen otras vías de acceso, por ejemplo las que utilizan los delincuentes que se dedican a realizar butrones.
 Por eso mismo un sistema UNIX Like puede ser inseguro, y un Windows puede ser relativamente seguro, todo dependerá del usuario tras el monitor, y las medidas y políticas que este lleve a cabo en el uso de todo dispositivo, desde su propio PC hasta el Router, pasando por los cables STP o UTP que distribuydifen la conexión entre los diferentes dispositivos de la casa u oficina, y finalmente el factor suerte y sus hábitos.
Por eso mismo un sistema UNIX Like puede ser inseguro, y un Windows puede ser relativamente seguro, todo dependerá del usuario tras el monitor, y las medidas y políticas que este lleve a cabo en el uso de todo dispositivo, desde su propio PC hasta el Router, pasando por los cables STP o UTP que distribuydifen la conexión entre los diferentes dispositivos de la casa u oficina, y finalmente el factor suerte y sus hábitos.
Lo que hay que tener siempre en cuenta es que si queremos estar relativamente seguros utilizando un Sistema Operativo privativo, y además mal hecho deberemos estar dispuestos a desembolsar grandes cantidades de dinero, ya que deberemos comprar los paquetes de Software y el Hardware que nos indiquen, sin dejarnos mucha libertad de elección, para realizar tareas que podríamos llevar a cabo de forma gratuita con Software Libre de la misma calidad o incluso superior en muchísimos casos.
 Ya que en vez de una empresa que solo piensa en sus ingresos, este está desarrollado por una gran comunidad de usuarios como nosotros, pensando en lo que necesitan para sí mismos.
Ya que en vez de una empresa que solo piensa en sus ingresos, este está desarrollado por una gran comunidad de usuarios como nosotros, pensando en lo que necesitan para sí mismos.
 Esta gran diferencia la explica muy bien Eric S. Raymond en su libro La Catedral y el Bazar, disponible su versión en Español en la categoría de Software Libre de la Biblioteca del blog.
Esta gran diferencia la explica muy bien Eric S. Raymond en su libro La Catedral y el Bazar, disponible su versión en Español en la categoría de Software Libre de la Biblioteca del blog.
Por ejemplo si utilizamos un sistema operativo privativo como Windows, y acatamos todas las recomendaciones de los expertos en seguridad de la información y seguridad en redes, pagamos por las actualizaciones rápidamente cada vez que estas salen al mercado, disponemos de acceso 24/7 a un servicio técnico, pero hacemos caso omiso a algunas de las recomendaciones, nos relajamos y por ejemplo descargamos un juego crackeado, no servirá de nada todo lo demás que hagamos para salvaguardar nuestro sistema, ya que somos nosotros mismos quienes estamos instalando el malware.
 No es que quiera decir que debáis pagar para utilizarlo, ni espero que os llevéis las manos a la cabeza, pero hay que tener en cuenta los riesgos que conlleva cada acción que vayamos a tomar, para hacerlo de forma segura, y es nuestra responsabilidad formarnos como usuarios, saber que herramientas están a nuestra disposición, y utilizarlas, darlas a conocer, y compartirlas.
No es que quiera decir que debáis pagar para utilizarlo, ni espero que os llevéis las manos a la cabeza, pero hay que tener en cuenta los riesgos que conlleva cada acción que vayamos a tomar, para hacerlo de forma segura, y es nuestra responsabilidad formarnos como usuarios, saber que herramientas están a nuestra disposición, y utilizarlas, darlas a conocer, y compartirlas.
Si te ha gustado puedes seguirme en Twitter, Facebook, Google+ o compartirlo con los botones ubicados debajo de esta publicación.



![BCN Raspberry JAM – Sistemas de videovigilancia libres [14/11/15]](http://www.peatonet.com/wp/wp-content/uploads/2015/11/Captura-de-pantalla-de-2015-11-18-113251-150x150.png)
![De la ética hacker al movimiento maker – la cultura del hacer [Valentín Muro]](http://www.peatonet.com/wp/wp-content/uploads/2014/09/47cbd8_HackerHand_foto_web-700x450-150x150.jpg)