Ayer decidí que la entrada de hoy se la reservaría a la red Tor. Pensé en explicar como se instala, configura, y utiliza, todo ello bajo Ubuntu GNU/Linux.
A la hora de navegar por TOR me arrepentí, luego os contaré porque.
Vamos con un min-análisis de TOR:
Tor es una red basada en proxys, que básicamente nos ofrece navegar de forma anónima, y con salida a Internet, funciona por capas de proxys cifrados, que se tunelizan unos encima de otros, el esquema perfecto sería una cebolla, por sus capas. De ahí el iconito de la cebolla en vidalia (luego veremos que es) y lo del dominio .onion (cebolla en Inglés).
Es básicamente un servicio que se ejecuta en segundo plano (un demonio en nuestro caso, ya que trabajamos en GNU/Linux) que se suele combinar con un servidor local y un cliente proxy, para que toda salida a Internet sea canalizada hacia Tor.
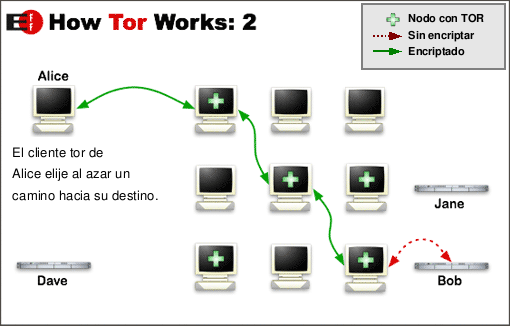
Nuestra conexión, será canalizada a través de nuestro proxy local hacia un nodo TOR, y pasando por varios nodos TOR, llegará a un punto en que de uno de esos nodos, volverá a Internet. En el siguiente esquema podemos ver como funciona de una forma mas visual:
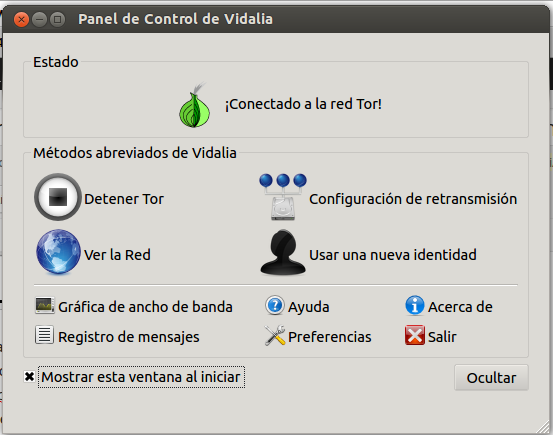
Para gestionar el arranque, parada, reinicio y configuración de este servicio/demonio disponemos de los típicos comandos para servicios (service tor stop/start/restart) también existe Vidalia, una interfaz gráfica que permitirá a todo tipo de usuarios velar por su seguridad/anonimato de una forma rápida, y que no requiere precisamente conocimientos técnicos avanzados.
Android tiene su versión de esa interfaz gráfica, llamada Orbot.
También disponemos de distribuciones LiveCD de Ubuntu optimizadas para el anonimato, que implementan TOR entre otras herramientas, como por ejemplo Tails.
Normalmente como proxy se utiliza privoxy, ya que es muy fácil de configurar, pero si queremos que el proxy nos haga también la función de proxy caché (suele ser deseable debido a la poca velocidad de esta red anónima) y nos guarde las webs que vamos solicitando por un tiempo determinado, optaremos por pólipo.
Finalmente, instalaremos un cliente proxy en nuestro navegador, e iremos a la siguiente web para comprobar que nuestro trafico saliente (al menos el del navegador) está saliendo por la pasarela TOR.
https://check.torproject.org/
Esta red permite trabajar de forma anónima desde cualquier programa que disponga de herramientas para configurar los parámetros de red, y soporte proxy http o socks v5 (véase navegadores web, clientes IRC, clientes de correo tipo Outlook Express o Mozilla Thunderbird, etc..).
Como antes decía, ayer pensé en escribir algo mas “imitable”, un tutorial paso a paso para configurar TOR bajo Ubuntu. Cuando me adentré en la deep web (web profunda) de la que Tor forma parte, cambié de idea rápidamente.
Ese cambio de idea se dio al ver, y así recordar, lo que allí abunda: asesinos a sueldo, fabricantes de sustancias prohibidas, venta de armas, venta de títulos universitarios, e incluso, y esto es de lo que mas hay, y lo que mas arcadas me produce, pederastas y/o pedófilos.
Y me dí cuenta de que en cierta medida, las personas que puedan llegar a leer este blog y sientan curiosidad, encontrarán innumerables entradas en la primera página de su búsqueda en cualquier browser, en las que podrán encontrar tutoriales paso a paso mas o menos actualizados, con los que podrán instalar TOR y experimentar con el, eso si… si vais a entrar en TOR, mejor desactivad la opción de cargar imágenes automáticamente en los sitios web, así evitaréis visualizar imágenes desagradables.
Como en el país en el que vivo (España), no veo todavía urgencia en usar este tipo de servicios, el lector tomará su tiempo si lo desea en buscarse un buen tutorial, y poder instalar lo que ya comprende mas (o menos) después de esta lectura introductoria.
Así me ahorraré un típico: el autor del blog no se responsabiliza del uso que se le dé al contenido del mismo, para cuando pueda hacerme mas falta.
En la siguiente entrega de Diario de un Onionauta, podréis ver una reflexión mas a fondo de lo que he encontrado en este buceo entre capas cebollunas.
Hasta mas cruzarnos…
Si te ha gustado puedes seguirme en Twitter, Facebook, Google+, Linkedin, o compartirlo con los botones ubicados debajo de esta publicación, si tienes cualquier pregunta o sugerencia no dudes en comentar.
![BCN Raspberry JAM – Sistemas de videovigilancia libres [14/11/15]](http://www.peatonet.com/wp/wp-content/uploads/2015/11/Captura-de-pantalla-de-2015-11-18-113251-150x150.png)


![La redacción de Diario de: TOR – La red invisible [Cuatro]](http://www.peatonet.com/wp/wp-content/uploads/2014/08/53da2538d70fb-660x371-150x150.jpg)








